In today’s hyperconnected business environment, APIs (Application Programming Interfaces) have become the backbone of digital transformation. From mobile banking apps to e-commerce platforms, APIs enable the seamless data exchange that modern Saudi enterprises depend on. However, this connectivity comes with significant API security risks that organizations can no longer afford to ignore.
According to recent industry reports, 57% of organizations experienced API-related data breaches in the past two years, with 99% facing at least one API security issue. For Saudi businesses operating under strict regulatory frameworks like SAMA, NCA, and PDPL, implementing robust API security measures isn’t just a best practice, it’s a compliance imperative.
Why API Security Matters for Saudi Enterprises
Saudi Arabia’s Vision 2030 has accelerated digital transformation across every sector. Banks are launching digital-first services, healthcare providers are implementing telemedicine platforms, and government entities are digitizing citizen services. At the heart of all these initiatives are APIs and they’ve become prime targets for cybercriminals seeking to exploit API security vulnerabilities.
The statistics paint a concerning picture:
- Over 1.6 billion records were exposed through API breaches in 2024 alone
- Only 21% of organizations can effectively detect attacks at the API layer
- DDoS attacks, fraud, and brute force remain the top API security threats
- 65% of organizations believe AI applications introduce new API security risks
Common API Security Vulnerabilities

Understanding the threat landscape is the first step toward effective API security. Based on the OWASP API Security Top 10 and recent breach analyses, here are the most critical vulnerabilities:
- Broken Authentication and Authorization Weak authentication mechanisms allow attackers to impersonate legitimate users. Implementing OAuth 2.0 and JWT tokens with proper validation is essential for any API security strategy.
- Excessive Data Exposure APIs often return more data than necessary, exposing sensitive information. Only 19% of organizations are confident they know which APIs expose personally identifiable information (PII).
- Shadow and Zombie APIs Undocumented or deprecated APIs that remain active create significant API security blind spots. Complete API discovery and inventory management is crucial.
- Third-Party API Risks Organizations now utilize an average of 131 third-party APIs, yet only 16% report high capability to mitigate these external risks.
API Security Best Practices for SAMA and NCA Compliance
For Saudi organizations subject to SAMA, and NCA, API security must align with specific compliance requirements:
Implement Strong API Authentication Use multi-factor authentication (MFA) for API access, implement rate limiting to prevent brute force attacks, and deploy API gateways with built-in security controls. SAMA’s Cybersecurity Framework specifically requires robust authentication for all digital services.
Enable API Encryption and Data Protection Encrypt data in transit and at rest using industry-standard protocols. SAMA guidelines require AES or RSA encryption for financial data, with strict key management practices.
Deploy Real-Time API Monitoring Implement continuous API monitoring with real-time alerts for suspicious activities. NCA’s Essential Cybersecurity Controls (ECC) mandate logging and monitoring of all critical systems.
Conduct Regular API Security Testing Integrate API security testing into your CI/CD pipeline. Regular vulnerability assessments and penetration testing help identify weaknesses before attackers do.
How to Choose the Right API Security Solution
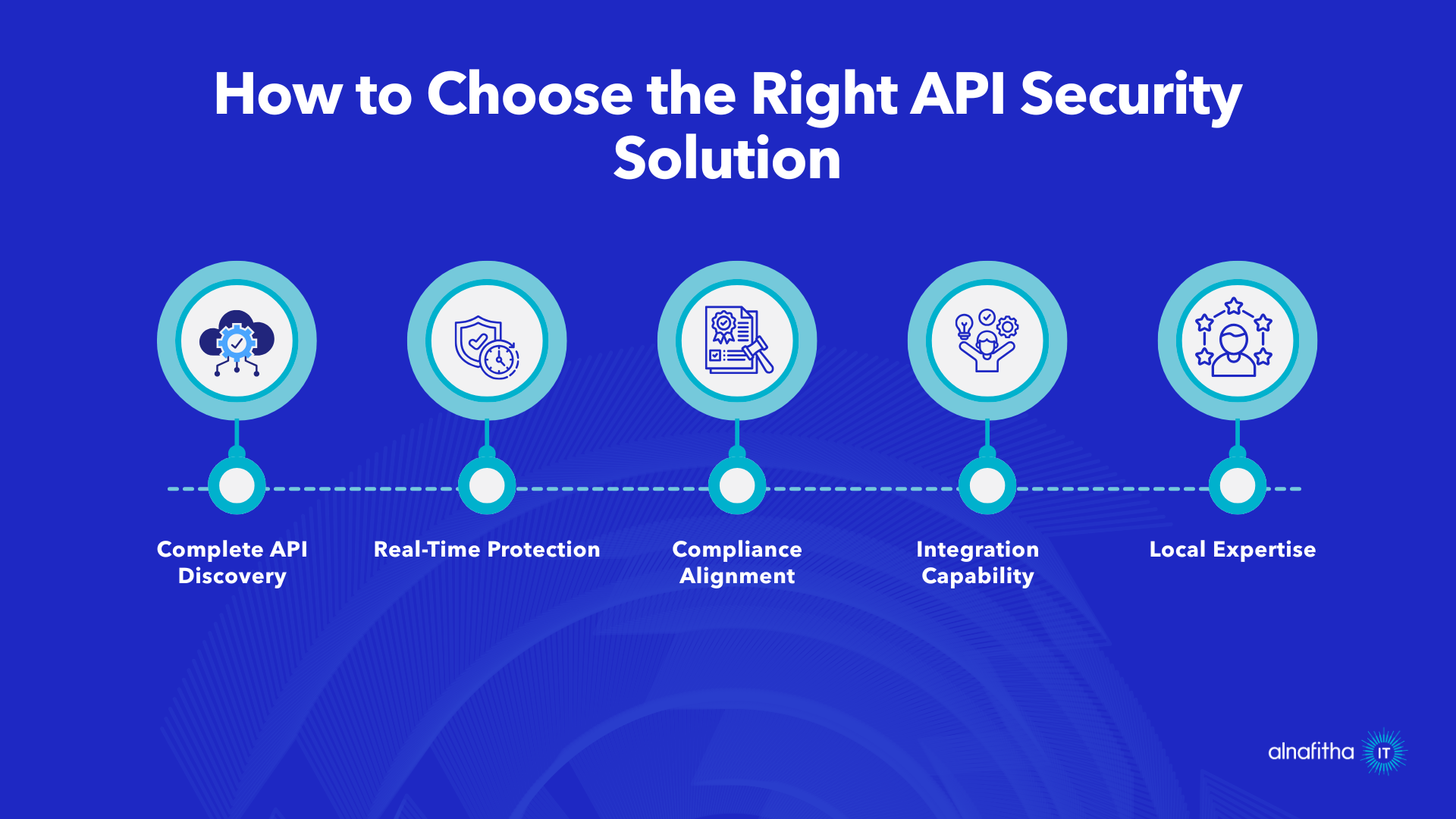
When evaluating API security solutions for your Saudi enterprise, consider:
- Complete API Discovery: Can it find all APIs, including shadow and zombie APIs?
- Real-Time Protection: Does it detect and block threats as they happen?
- Compliance Alignment: Is it designed for SAMA, NCA, and PDPL?
- Integration Capability: Will it work with your existing security stack?
- Local Expertise: Does the provider understand the Saudi market?
Alnafitha IT: Your API Security Partner
With over 30 years of experience in the Saudi IT market and 7,000+ satisfied clients, Alnafitha IT delivers full scale API security solutions through partnerships with Zscaler, Palo Alto, F5, Netskope, and Fortinet.
Our API security approach includes:
- Complete API discovery and inventory management
- Real-time threat detection using AI-driven anomaly detection
- API gateway implementation with built-in security features
- Full compliance alignment with SAMA and NCA frameworks
- 24/7 Security Operations Center (SOCaaS) monitoring
- Vulnerability assessment and penetration testing (VAPT)
Conclusion
As APIs continue to power Saudi Arabia’s digital transformation, securing them is no longer optional — it’s a business imperative. From protecting sensitive data to meeting SAMA and NCA compliance requirements, a strong API security strategy is essential for any organization operating in today’s threat landscape.
Secure Your APIs Today
API security isn’t just about protecting endpoints, it’s about safeguarding your entire digital ecosystem. Don’t wait for a breach to expose your vulnerabilities. Gain the visibility, protection, and compliance alignment your business needs.
Ready to strengthen your API security posture?
Contact Alnafitha IT today for a free consultation.
