Regulatory pressure around NCA ECC compliance has intensified since the National Cybersecurity Authority released ECC-2:2024 its most significant update to the Essential Cybersecurity Controls framework since the original 2018 publication. For compliance officers, risk managers, and auditors at Saudi government entities and Critical National Infrastructure operators, the question is no longer whether to comply. The question is whether your current processes can prove it.
Most organizations in the Kingdom are still relying on fragmented, manual workflows to track access changes, collect audit evidence, and produce compliance reports. When an NCA assessment window opens, teams scramble to reconstruct months of activity from disconnected logs, spreadsheets, and email threads. That approach does not hold up to scrutiny, and with ECC-2 tightening requirements across 110 controls spanning governance, defense, resilience, third-party management, and industrial controls, the exposure from inadequate documentation is growing.
This article explains what NCA ECC compliance specifically demands from a technical controls perspective, where most organizations fall short, and how ManageEngine ADAudit Plus and Log360, deployed and supported by Alnafitha IT, convert those requirements into automated, auditable processes.
What NCA ECC-2:2024 Compliance Actually Demands
The ECC-2:2024 framework applies to all Saudi government ministries, authorities, and affiliated entities, as well as private sector organizations that own, operate, or host Critical National Infrastructure. This includes sectors such as financial services, telecommunications, energy, and healthcare.
The framework is structured across four main domains:
- Cybersecurity Governance: strategy, policy, and organizational structure
- Cybersecurity Defense: identity management, access controls, endpoint and network security, and data protection
- Cybersecurity Resilience: backup, business continuity, and incident response
- Third-Party and Cloud Cybersecurity: vendor management and cloud service controls
ECC-2 introduced notable changes from the original version. The number of controls was rationalized from 114 down to 110 to improve implementation efficiency. The framework also expanded Saudization requirements for cybersecurity roles: all cybersecurity positions must now be filled by qualified Saudi professionals on a full-time basis, not just senior roles as was the case under ECC-1. Data localization requirements have been transferred from ECC to the National Data Management Office (NDMO), but this does not ease actual data handling obligations.
For auditors and compliance teams, the continuous compliance mandate is the critical operational challenge. NCA does not expect a snapshot of compliance taken once a year. Organizations must demonstrate ongoing adherence which requires real-time monitoring, consistent log retention, and evidence that controls are functioning as intended across every reporting period.
Where NCA ECC Compliance Breaks Down in Saudi Organizations
Four pain points consistently cause NCA ECC compliance gaps in Saudi organizations:
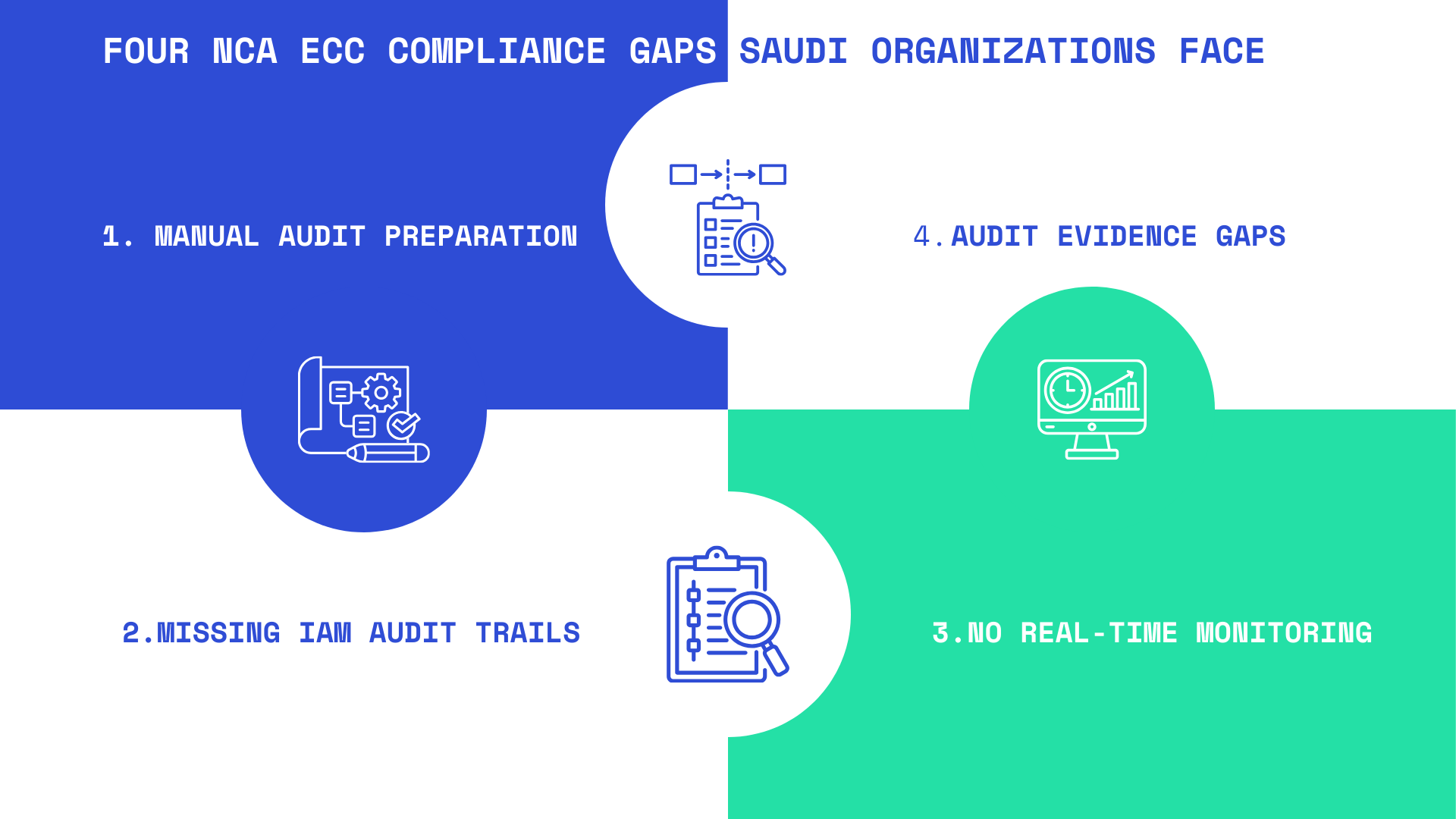
1. Manual Audit Preparation Delays NCA ECC Compliance
When an assessment approaches, teams spend weeks pulling logs from Active Directory, servers, firewalls, and cloud environments. Without a unified collection and normalization layer, the process introduces human error and creates significant gaps between what the framework requires and what the organization can actually demonstrate.
2. IAM Documentation Gaps That Fail NCA ECC Compliance Audits
ECC Domain 2 places heavy requirements on identity management: role-based access control, privilege management, multi-factor authentication enforcement, and timely de-provisioning of access. Without continuous AD auditing, organizations cannot prove that these controls were consistently applied, not just configured at a point in time.
3. Absence of Real-Time Monitoring
ECC requires organizations to monitor for security events and respond to threats as part of their ongoing defense posture. Periodic log reviews do not satisfy this requirement. Auditors look for evidence of active monitoring, alert thresholds, and documented response actions.
4. Evidence Collection and Reporting
Producing structured, formatted compliance reports that map directly to NCA ECC control references is a time-consuming task when done manually. The absence of pre-built compliance report templates means teams often produce inconsistent outputs that are difficult for auditors to interpret.
How ADAudit Plus and Log360 Address NCA ECC Compliance Requirements
ManageEngine ADAudit Plus and Log360 are purpose-built for the exact compliance and monitoring requirements that ECC-2 mandates. Together, they cover identity and access auditing, real-time event monitoring, SIEM correlation, and automated compliance reporting across hybrid environments.
ADAudit Plus: Continuous Active Directory Auditing for ECC Domain 2
ADAudit Plus provides real-time auditing of Active Directory, Microsoft Entra ID (Azure AD), file servers, Windows servers, and workstations. For NCA ECC compliance, the most relevant capabilities include:
- Immediate alerts on privileged account changes, group policy modifications, and user permission escalations
- User behavior analytics (UBA) that flag anomalous access patterns a direct input into ECC incident detection requirements
- File server auditing tracking who accessed, modified, or deleted sensitive data and when
- Detailed logon/logoff tracking across workstations with failure analysis for lockout investigations
- Pre-built compliance reports for access governance, including evidence formatting suitable for NCA assessments
For organizations managing Microsoft Entra ID environments alongside on-premises AD, ADAudit Plus covers both surfaces in a single console, providing audit trails that span the full identity boundary without manual reconciliation.
Log360: Unified SIEM for Continuous ECC Compliance Monitoring
Log360 is ManageEngine’s unified SIEM platform, combining the capabilities of ADAudit Plus, EventLog Analyzer, Cloud Security Plus, O365 Manager Plus, and Exchange Reporter Plus into a single solution. This matters for NCA ECC compliance because the framework does not silo its requirements; it demands coordinated visibility across the entire technology environment.
Log360 delivers:
- Centralized log collection from Windows and Linux systems, network devices, databases, web servers, and cloud infrastructure (AWS, Azure, GCP)
- Out-of-the-box compliance reports aligned with Saudi regulatory frameworks including SAMA the foundation for mapping to NCA ECC control domains
- SOAR (Security Orchestration, Automation and Response) capabilities for automated incident workflows and ticket creation, providing documented response evidence for ECC resilience controls
- UEBA (User and Entity Behavior Analytics) for detecting insider threats and compromised credentials in real time
- CASB integration for visibility into cloud application usage relevant to ECC cloud security controls
The combination of ADAudit Plus and Log360 means that every change in the identity and access layer is captured, every log event is normalized and stored, every anomaly is flagged in real time, and every compliance report is ready to generate on demand. That directly addresses the four pain points that cause most Saudi organizations to fail NCA ECC audits.
Deploying NCA ECC Compliance Solutions in Saudi Enterprises

Technology solutions that address NCA ECC compliance requirements are only as effective as the implementation behind them. Saudi organizations dealing with on-premises infrastructure, hybrid cloud environments, and strict data handling requirements need a partner who understands both the technical architecture and the local regulatory landscape.
Alnafitha International has been operating in the Saudi IT market since 1993 and holds deep expertise in ManageEngine solution deployment. As a certified ManageEngine partner, Alnafitha’s team configures ADAudit Plus and Log360 to map directly against ECC control domains, ensuring that compliance reporting is accurate from day one rather than requiring months of post-deployment tuning.
The implementation approach covers:
- Gap assessment against ECC-2:2024 control domains before deployment
- Configuration of audit policies aligned with NCA monitoring requirements
- Custom report templates mapped to ECC control references for direct use in NCA assessments
- Ongoing support to maintain compliance posture as the framework evolves
For organizations in financial services, government, or telecom sectors facing the most intensive NCA ECC compliance scrutiny, working with a partner who understands both ManageEngine’s capabilities and the NCA framework is the difference between a successful audit and a costly remediation cycle.
You can explore Alnafitha’s full range of ManageEngine solutions available for Saudi enterprises at alnafitha.com.
For authoritative reference, the current ECC-2:2024 framework documentation and implementation guidance are published directly by the National Cybersecurity Authority (NCA). Organizations seeking implementation methodology can also reference the NCA Guide to ECC Implementation which outlines specific technical and organizational steps for each control domain.
Conclusion
NCA ECC compliance is not a project with a finish line. It is a continuous operational requirement that demands consistent monitoring, automated evidence collection, and audit-ready reporting at all times. For Saudi government entities and CNI operators, the ECC-2:2024 framework makes this expectation explicit.
ManageEngine ADAudit Plus and Log360 provide the technical foundation to meet these requirements without overburdening compliance teams with manual processes. When implemented correctly, they convert NCA ECC compliance from a periodic scramble into a documented, defensible, ongoing program.
Alnafitha’s experience deploying these solutions across Saudi enterprises means your implementation is built for your regulatory environment, not adapted from a generic global template.
Close your NCA ECC compliance gaps
Request a consultation with Alnafitha’s compliance specialists and get a custom implementation roadmap for your organization.
