Most organizations across Saudi Arabia understand that cybersecurity has changed. What fewer have acted on is how fundamentally the architecture of security itself needs to change. The zero trust security model is not a product upgrade or a policy revision. It is a structural shift in how trust is assigned, verified, and continuously enforced across every user, device, and application in your environment.
In 2026, with NCA enforcement regulations now carrying fines up to SAR 25 million and SAMA audits actively scrutinizing identity controls, the question for Saudi CISOs is no longer whether to adopt the zero trust security model, but how fast and with which partner.
What Is the Zero Trust Security Model?
The zero trust security model is a security framework built on a single operating principle: never trust, always verify. Unlike traditional perimeter-based security, which assumes that anyone inside the corporate network is safe, zero trust treats every access request as a potential threat, regardless of where it originates.
The concept was formalized by NIST Special Publication 800-207, which defines Zero Trust Architecture (ZTA) as a set of guiding principles for workflow, system, and network design. In practice, it means that no user, device, or workload earns standing trust. Every session is evaluated based on identity, device posture, behavior, and context, before access is granted.
For Saudi enterprises managing hybrid workforces, cloud migrations, and third-party vendor access simultaneously, the zero trust security model is the only architecture that addresses all three exposure vectors at once.
What Are the 7 Pillars of the Zero Trust Security Model?
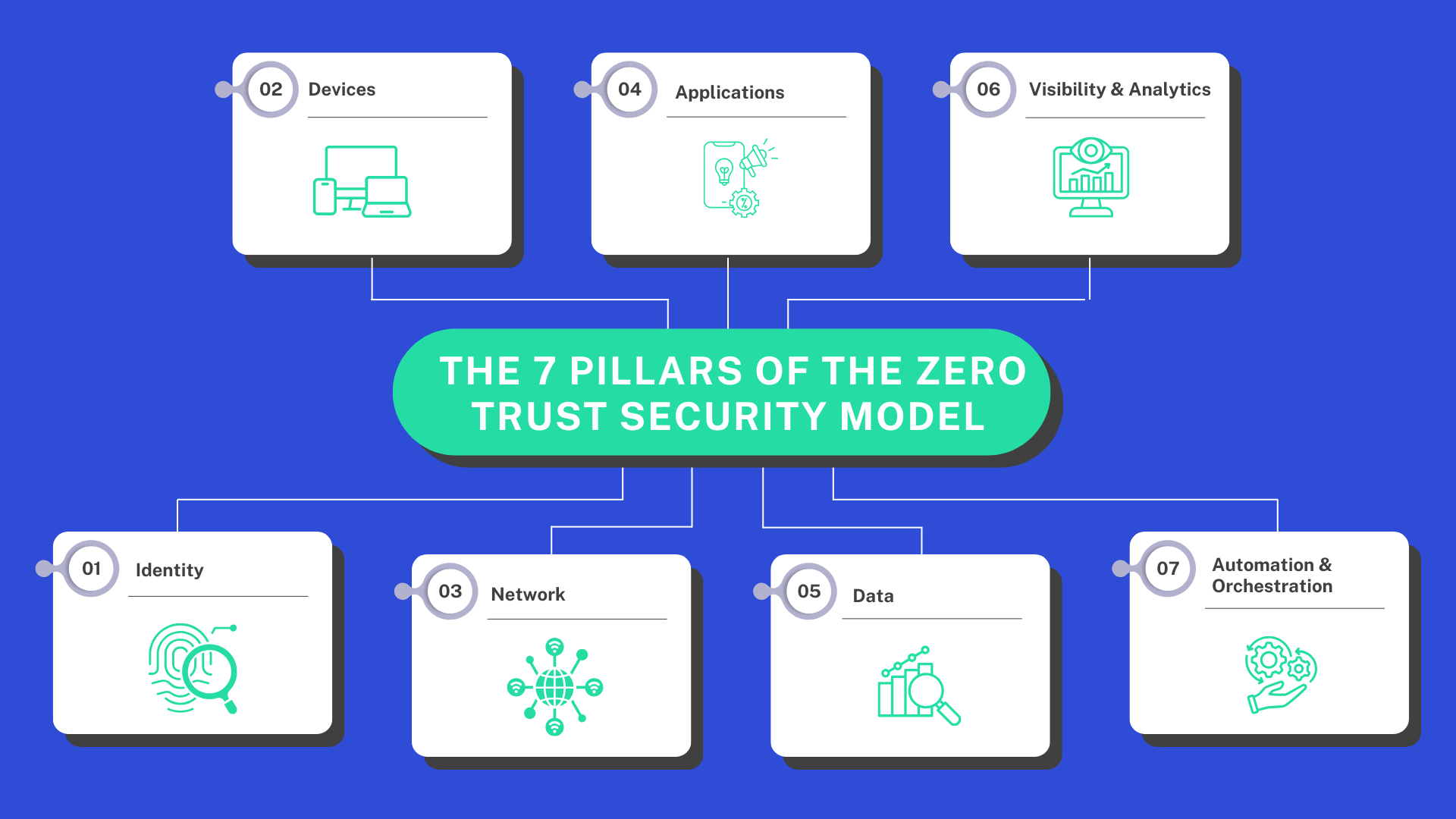
The most widely referenced framework for operationalizing the zero trust security model is built around seven pillars. Each pillar maps directly to a control domain, and together they address the full surface area of enterprise risk:
- Identity: Every user and service account is continuously verified, not trusted by default.
- Devices: Only compliant, managed devices gain access, regardless of network location.
- Network: Micro-segmentation replaces flat network access. Lateral movement is blocked by design.
- Applications: Access is granted per application, not per network segment. ZTNA makes this operational.
- Data: Data is classified, monitored, and protected wherever it moves, including cloud environments.
- Visibility & Analytics: Continuous monitoring generates the audit trails NCA and SAMA inspectors now actively review.
- Automation & Orchestration: Policy enforcement scales without manual intervention, reducing the human error margin.
For organizations aligning with NCA ECC-2:2024, pillars 1, 3, and 6 are the most directly auditable. SAMA’s Identity and Access Management requirements connect most tightly to pillars 1, 4, and 7.
Is ZTNA Replacing VPN? What Saudi Organizations Need to Know
This is one of the most searched questions in the Saudi market right now, and the answer is: yes, ZTNA is replacing VPN, and for good reason.
A traditional VPN grants a user full network access once they authenticate. That means a compromised contractor credential or a poorly segmented vendor connection can expose the entire internal environment. This directly contradicts the least-privilege access principle that both NCA and SAMA require.
Zero Trust Network Access (ZTNA) works differently. Instead of connecting a user to the network, ZTNA connects them to a specific application, on a per-session basis, after verifying identity, device health, and contextual signals. If the session behavior changes, access is re-evaluated or terminated.
For Saudi enterprises with distributed workforces across Riyadh, Jeddah, and Dammam, and with employees working from outside the Kingdom, ZTNA solves the access problem that VPN was never designed to handle at this scale or this risk level.
The Four Access Risks That the Zero Trust Security Model Directly Solves
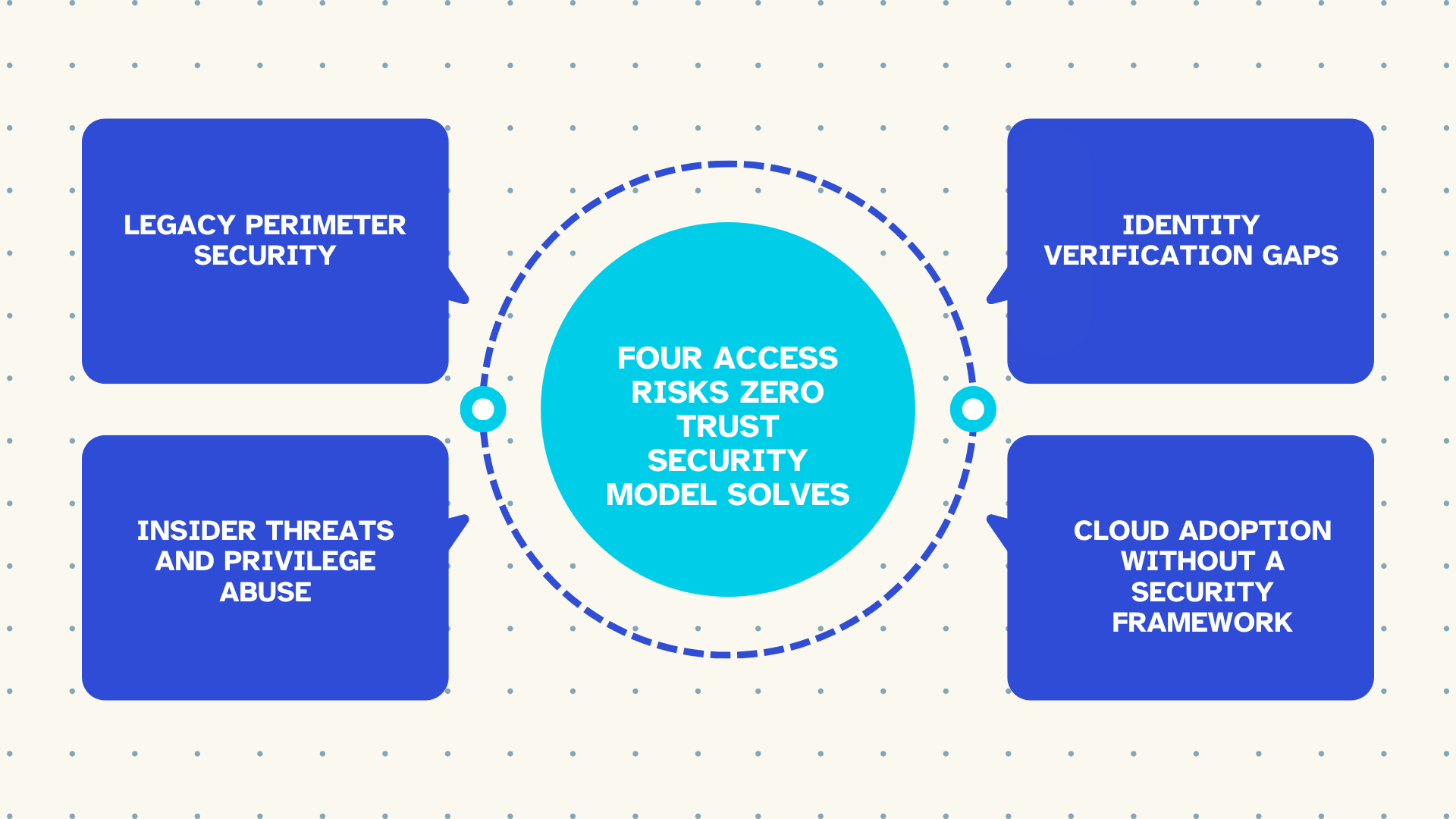
Legacy Perimeter Security
The old model assumed a clearly defined network boundary. Cloud adoption has made that boundary meaningless. The zero trust security model eliminates the perimeter assumption entirely and secures access at the identity and application layer instead.
Insider Threats and Privilege Abuse
This is the highest-risk exposure category for large Saudi enterprises and financial institutions. Whether the threat comes from an over-permissioned employee, a dormant service account, or a third-party vendor with excessive rights, zero trust’s continuous verification and least-privilege enforcement closes the window before damage occurs.
Identity Verification Gaps
Single-point authentication at login is not sufficient. Open sessions represent live, unmonitored risk. Conditional access policies within the zero trust security model re-verify continuously, flagging anomalies that static authentication systems never see.
Cloud Adoption Without a Security Framework
Rapid cloud migration across Azure, AWS, and Microsoft 365 without an identity-aware security layer creates unaccounted gaps. Zero trust architecture is cloud-native by design, making it the correct security framework for organizations in the middle of digital transformation, not after it is complete.
How the Zero Trust Security Model Maps to NCA ECC-2:2024 and SAMA Requirements
Saudi regulators do not mandate the term ‘zero trust’ by name. But the NCA’s updated Essential Cybersecurity Controls (ECC-2:2024) and SAMA’s Cybersecurity Framework both require the exact technical controls that the zero trust security model delivers:
NCA ECC-2:2024 requires organizations to demonstrate real-time access control, continuous monitoring, privileged access management, and audit-ready evidence of identity governance. The December 2024 enforcement regulations mean non-compliance now triggers fines and license consequences, not just advisory notices.
SAMA’s framework for financial institutions specifically calls for robust Identity and Access Management, segregation of duties, and access logging across all systems handling financial data. These are not aspirational guidelines. They are auditable requirements that zero trust architecture satisfies by design.
For the complete NCA control reference, visit the NCA official cybersecurity controls portal.
How to Implement the Zero Trust Security Model: Where Saudi Enterprises Should Start
The most common mistake in zero trust adoption is treating it as a big-bang transformation. The organizations that succeed start with a focused scope and expand systematically. For most Saudi enterprises, the right starting point is identity.
Begin by mapping every identity in your environment, including service accounts, third-party vendor accounts, and privileged users. Enforce MFA across all access paths. Layer conditional access policies that evaluate device compliance and session context. Then extend the model outward to applications, data, and network segmentation.
Implementation complexity varies significantly by sector. A financial institution in Riyadh with strict SAMA controls needs a different sequencing than a healthcare provider aligning with NCA. This is where a partner with direct Saudi market experience matters.
Managed Zero Trust Security Services for Saudi Arabian Enterprises: The Alnafitha Approach
Alnafitha IT has spent over 30 years building enterprise security infrastructure across Saudi Arabia’s most demanding regulated sectors. As Microsoft’s Country Partner of the Year 2025 for Saudi Arabia, we bring direct access to the technology stack that makes zero trust operationally viable at scale: Microsoft Entra ID for identity governance, Microsoft Defender for endpoint compliance, Azure AD Conditional Access for session-level control, and Microsoft Sentinel for continuous monitoring and audit readiness.
Our Secure Access Solutions are not point-product deployments. They are designed around your regulatory requirements, your existing infrastructure, and the specific risk profile of your organization. Whether you are a financial institution in Riyadh managing SAMA compliance, a government entity aligning with NCA ECC-2:2024, or an enterprise in Jeddah or Dammam beginning a cloud migration, we build the zero trust security model around your reality, not around a vendor’s reference architecture.
We offer both full managed implementations and phased advisory engagements, depending on where your organization sits in its security maturity journey.
Why Waiting Is No Longer an Option
Every organization that delays building a zero trust security model is operating on borrowed time. Regulatory enforcement is active. Threat actors are targeting exactly the identity and access gaps that zero trust is designed to close. And the organizations already ahead of this curve are not the ones that waited for an incident to justify the investment.
The architecture is proven. The compliance case is clear. The Saudi regulatory environment has made the business case for your board. The remaining variable is execution, and that is where the right partner makes the difference.
Assess Your Zero Trust Security Model Readiness Today
Alnafitha IT offers structured security assessments mapped directly to NCA ECC-2:2024 and SAMA requirements. Get a clear picture of where your access security gaps are and what it takes to close them. Talk to our security team today and start the conversation before your next regulatory review forces it.
